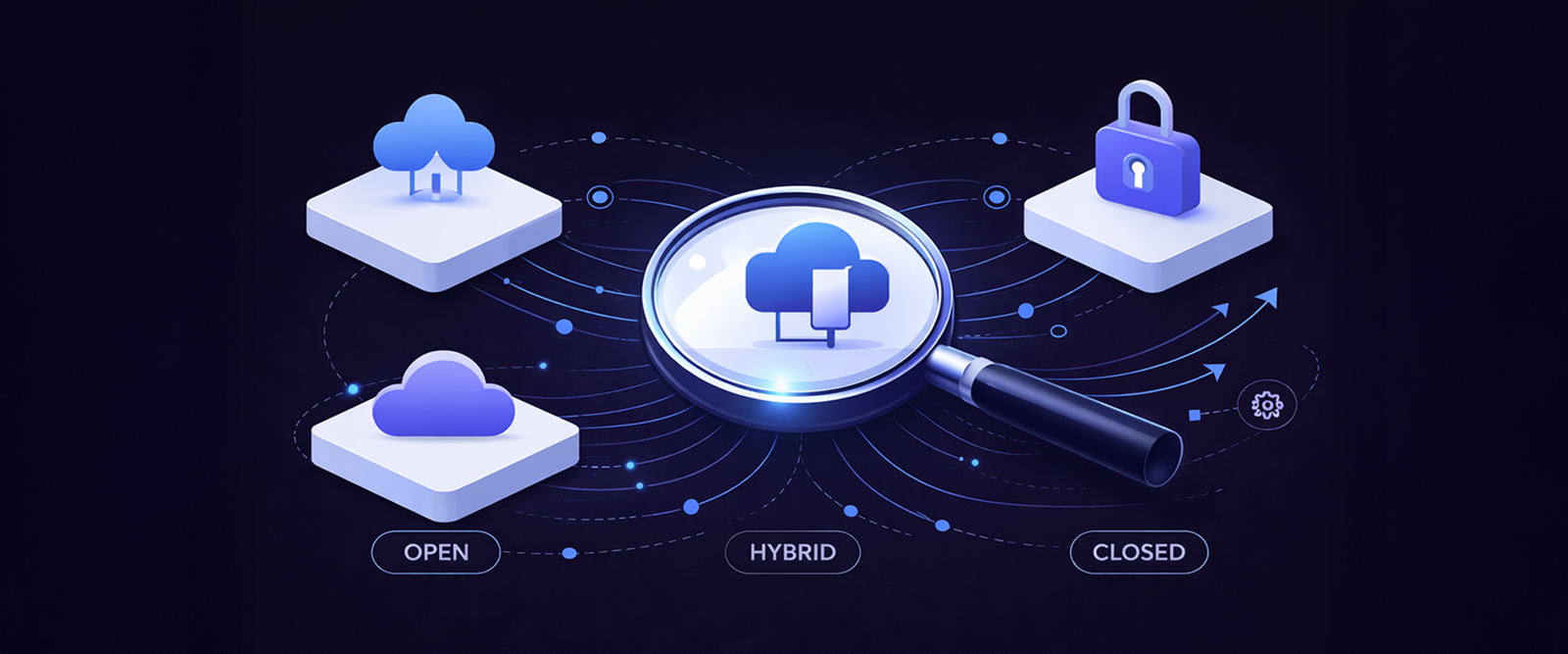
The transition to the SIEM++ era has forced a major architectural crossroads. Organisations must now choose between three distinct paths- the modular flexibility of Open systems, the seamless integration of Closed platforms, or the cost-optimised balance of Hybrid models. Before committing to a multi-year contract, security leaders must decode these architectures against their own operational maturity and data requirements.
- The Open Architecture ➔ Best-of-Breed & Modular
Open architectures prioritise vendor neutrality and data portability. They are built on the premise that no single vendor can be the best at everything, endpoint, identity, network, and cloud.
The engine- Powered by the open schema framework, which acts as a ‘lingua franca’ to normalise data from hundreds of disparate sources.
The advantage- Eliminates vendor lock-in. You can swap your EDR or firewall provider without rebuilding your detection logic.
The strategic tool- ‘Federated Search.’ This allows you to query data at the source (S3 buckets, SaaS logs) without ingesting it into a central SIEM, bypassing the ‘ingestion tax’ and respecting data sovereignty.
Best for- Mature SOCs with strong engineering teams who want a customised, high-performance stack.
- The Closed Architecture ➔ Converged & Unified
Commonly referred to as ‘Unified Security Platforms’ or XSIAM (Extended Security Intelligence and Automation Management), closed architectures bundle SIEM, XDR, SOAR, and UEBA into a single, proprietary ecosystem.
The engine- A unified, security-specific data model that allows for ‘machine-driven’ correlation across the vendor’s own sensors.
The advantage- Simplicity and speed. Everything ‘just works’ out of the box. It reduces the ‘cognitive load’ on analysts who otherwise have to switch between multiple consoles.
The strategic tool- ‘Agentic AI’. Tightly bundled data allows AI agents to autonomously plan and execute investigations with deeper contextual awareness of the internal ecosystem.
Best for- Organisations seeking to reduce operational complexity and achieve rapid time-to-value with a leaner staff.
- The Hybrid Architecture ➔ The Data Lake Balance
The hybrid model is increasingly viewed as the future of cost-efficient defense. It splits the workload: a Security Data Lake handles the ‘cold’ bulk telemetry, while the SIEM handles the ‘hot’ real-time detections.
The engine- A tiered storage strategy. Ingest 10-20% of high-fidelity logs (EDR, Firewall) into the SIEM for real-time alerting; dump the other 80-90% (Cloud audits, application logs) into a low-cost lake like Snowflake or S3.
The advantage- Economic efficiency. You can retain years of data for forensics and compliance for 40-60% less than a monolithic SIEM.
The strategic tool- ‘Tiered Storage.’ Detections run in the SIEM for immediate response, while the lake enables deep-dive, batch-analysis threat hunting and machine learning.
Best for- Large enterprises with massive data volumes that must balance real-time response with long-term forensic visibility.
Summary Comparison: Which One to Choose?
| Architecture | Primary Focus | Flexibility | Management Overhead | Cost Efficiency |
|---|---|---|---|---|
| Open | Vendor Agnostic | Highest | High (Requires Engineering) | High (Avoids Lock-in) |
| Closed | Ease of Use | Lowest | Low (Out-of-the-Box) | Medium (Premium Price) |
| Hybrid | Cost & Scale | Medium | Medium (Requires Routing) | Highest (Optimised TCO) |
The Commitment Check- Data Gravity & Sovereignty
Regardless of the model, you must account for Data Gravity. As your data mass grows, it becomes harder and costlier to move. A closed cloud-native SIEM may feel like a ‘black hole’ if you ever try to migrate out. Simultaneously, Data Sovereignty laws (GDPR, DORA) may mandate that data stays in-region, making Federated Search a near-requirement for global organisations to query data without moving it across borders.