The transition to a next-generation SIEM is a strategic pivot away from the log-aggregation models of the past toward an intelligence-driven, autonomous security architecture. Before committing to a new platform, every CISO must look beyond marketing claims to evaluate architectural viability and operational ROI.
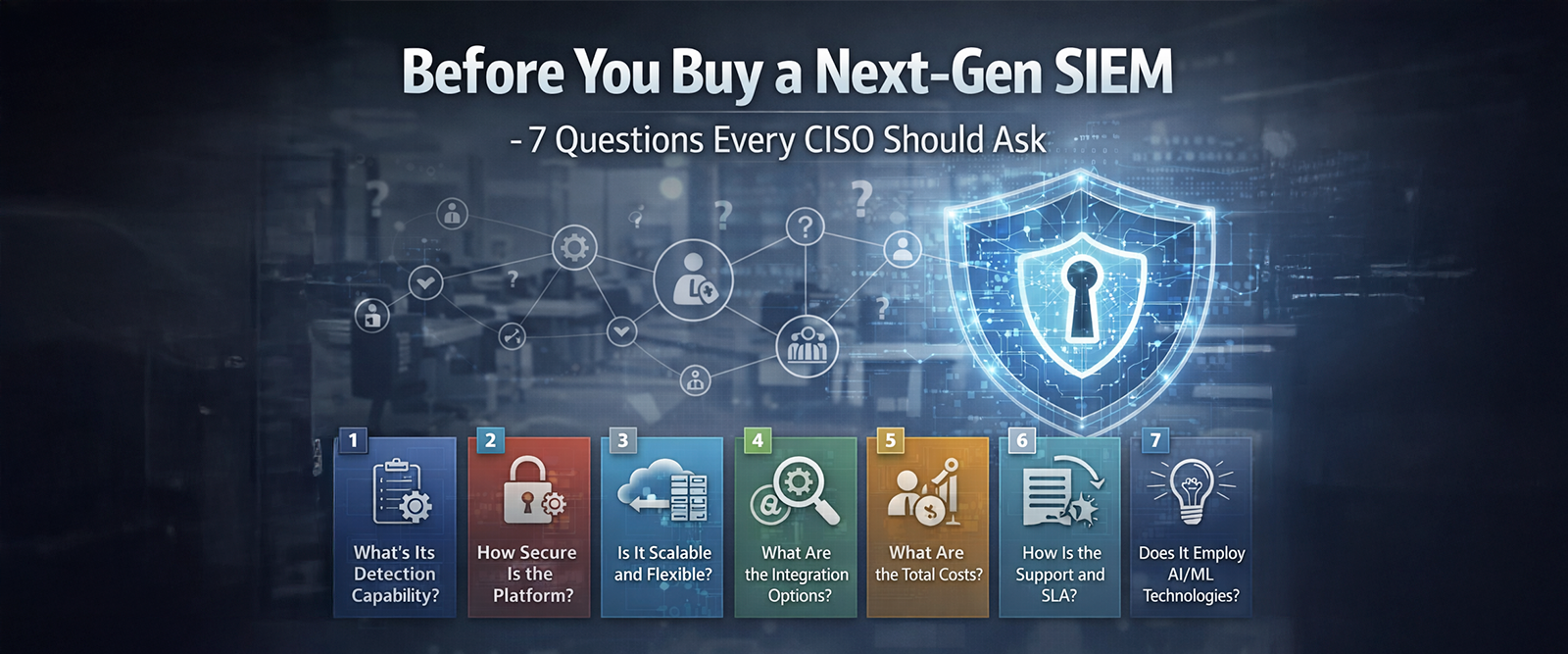
Here are seven critical questions to ask during the evaluation process:
- Is the architecture truly decoupled?
Next-gen SIEMs must separate compute power from storage. Ask if the platform allows you to store raw telemetry in a low-cost security data lake (like Amazon S3 or Google Cloud Storage) while only applying high-performance compute when needed for analysis. This decoupling is the only way to ensure long-term visibility without the ‘ingestion-based’ pricing that makes traditional SIEMs cost-prohibitive.
- Does it support open schema as a native schema?
Vendor lock-in is a primary failure point for legacy systems. Ensure the platform natively adopts the open schema framework. This allows you to write detection rules once and apply them across any vendor’s telemetry, future-proofing your security stack and reducing the manual labor of building custom parsers.
- Can I search data at the source without ingesting it?
The ‘centralise-everything’ model is obsolete. Ask if the platform supports Federated Search, which allows analysts to query data where it lives, such as in cloud buckets or SaaS applications, without moving it. This reduces latency, avoids massive ingestion fees, and respects data sovereignty laws like GDPR.
- Is the AI ‘Agentic’ or just a chatbot?
Distinguish between ‘AI trash’, simple chatbots that summarise alerts, and Agentic AI. Ask if the system can autonomously plan and execute investigations, synthesise evidence across disparate domains, and recommend response playbooks. Agentic systems move the needle by handling up to 90% of Tier-1 triage tasks, not just explaining what happened.
- What is the documented ‘Time to Productivity’ for new analysts?
Next-gen SIEMs should solve the talent shortage, not exacerbate it. Ask for data on how natural language interfaces reduce the time required for a junior analyst to become productive. Leading platforms have shown a 70% reduction in this ‘onboarding gap,’ allowing junior staff to handle 35% more security operations work previously reserved for seniors.
- Does it offer in-stream data processing?
Waiting for data to hit the database to detect a threat is too slow. Ask if the platform uses Security Data Pipelines (SDPP) to filter, deduplicate, and enrich logs in-stream. This identifies high-fidelity signals in real-time while dropping noisy heartbeats and health checks that drive up storage costs.
- What are the measurable impacts on MTTD and MTTR?
Security is measured in seconds, not hours. Require the vendor to provide evidence of how their automation and AI-driven correlation reduce MTTDand MTTR. Modern platforms target a 50-65% reduction in investigation and response times, effectively shrinking the blast radius of any potential breach.
Strategic Bottom Line- A next-generation SIEM should no longer be a cost center for log retention. It must be a strategic asset that defends the enterprise at machine speed. Asking these questions ensures your investment moves your SOC from a reactive alert queue to a proactive, autonomous command center.
If you are interested to know more, we would be happy to help