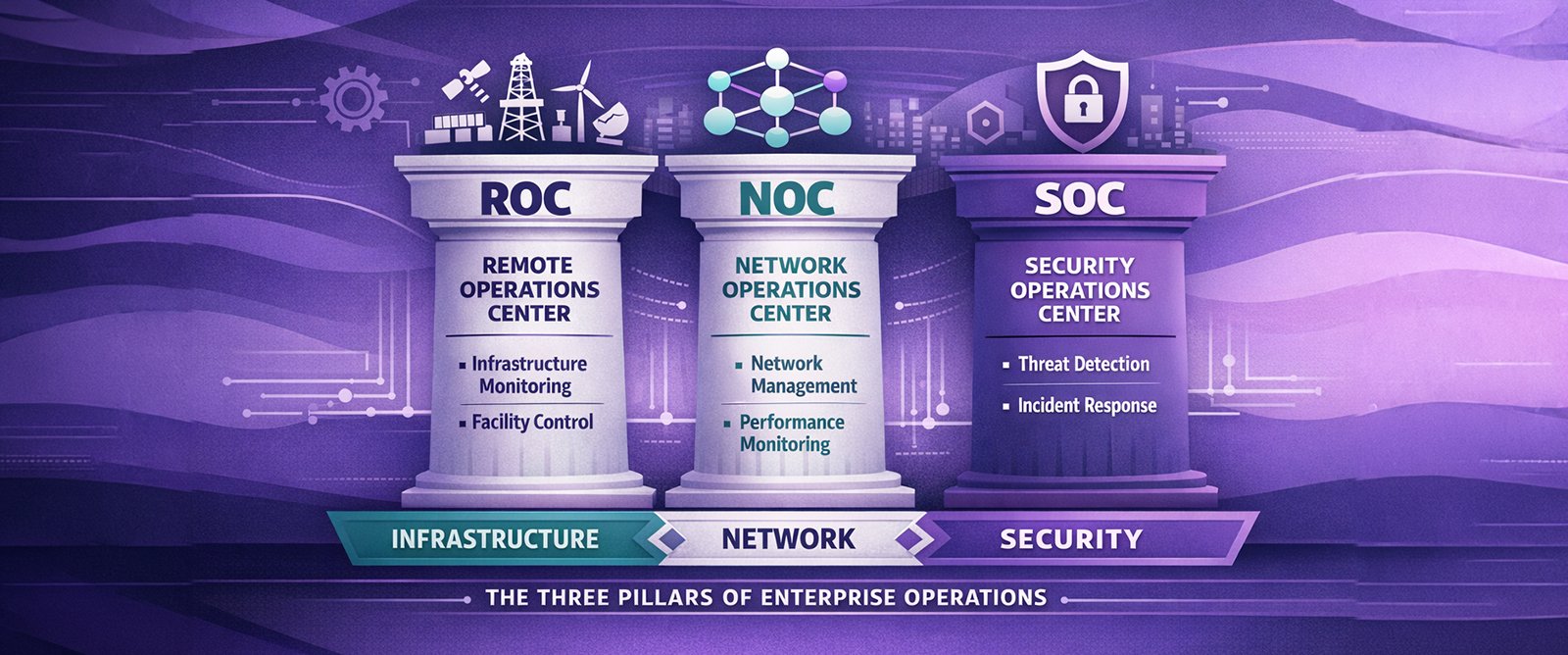
Enterprise operations have evolved into three distinct but deeply interconnected disciplines. Understanding the differences between your ROC, NOC, and SOC and how they must work together is foundational to building a resilient operational model.As enterprise IT environments have grown in complexity, the operational functions responsible for managing them have specialised. What was once a single “operations team” has evolved into distinct centres of excellence, each focused on a specific operational domain: the Resiliency Operations Centre (ROC), the Network Operations Centre (NOC), and the Security Operations Centre (SOC).Yet despite this specialisation, many enterprise leaders struggle to clearly articulate the boundaries between these functions, understand how they should interact, and determine how to invest across them effectively. The result is often duplication of effort, gaps in coverage, and organisational friction that slows incident response precisely when speed matters most.This guide provides a comprehensive breakdown of the ROC, NOC, and SOC: their distinct missions, capabilities, team structures, and tooling requirements. More importantly, it examines how these three pillars must integrate to deliver truly effective enterprise operations.
The Network Operations Centre (NOC)
Mission and Scope
The NOC is the nerve centre of IT infrastructure operations. Its primary mission is to ensure the availability, performance, and reliability of the organisation’s technology infrastructure: networks, servers, storage, cloud resources, databases, and the applications that run on them.NOC teams operate around the clock, monitoring the health of production environments, detecting and responding to incidents, managing changes, and maintaining the operational baselines that keep business-critical systems running. They are the first responders for infrastructure events and the primary owners of uptime and SLA compliance.
Core Capabilities
- Ingestion of all NOC and SOC data into a unified operational data lake
- AI-powered correlation across infrastructure, network, and security telemetry
- Cross-domain incident identification that neither the NOC nor SOC can detect in isolation
- Automated and AI-assisted resolution recommendations with clear prioritisation
- End-to-end incident ownership across multi-domain events spanning both NOC and SOC boundaries
- Continuous feedback loops to improve detection accuracy and resolution playbooks over time
Typical Team Structure
ROC teams combine deep expertise in AI and data engineering with strong operational backgrounds across both infrastructure and security domains. The team includes data engineers responsible for maintaining the operational data lake and ingestion pipelines, AI/ML engineers who build and refine the correlation and resolution models, and senior operations specialists who validate AI-generated insights and manage complex multi-domain incidents. The ROC is typically led by a Director or VP with visibility across both IT leadership and business leadership, given its role as the connective tissue of the entire operations model.
Key Differences: ROC vs NOC vs SOC
While all three centres are concerned with monitoring, detection, and response, their focal points and success criteria are fundamentally different.
- The NOC asks: “Is the infrastructure healthy and performing within acceptable parameters?” Its lens is technical, focused on uptime, latency, throughput, and error rates. Success is measured by availability percentages and MTTR for infrastructure incidents.
- The SOC asks: “Is the organisation protected against security threats?” Its lens is adversarial, focused on detecting and neutralising threats before they cause harm. Success is measured by detection coverage, response speed, and the absence of breaches.
- The ROC asks: “What is the full picture across infrastructure and security, and how do we resolve it?” Its lens is integrative, powered by AI. Success is measured by the accuracy of cross-domain correlation, speed of resolution, and the elimination of blind spots that exist when NOC and SOC operate in isolation.
Why Integration Matters More Than Separation
The most sophisticated enterprise operations models recognise that the ROC, NOC, and SOC cannot operate as isolated silos. Modern incidents rarely respect organisational boundaries. A security breach impacts infrastructure availability. An infrastructure outage can mask or trigger security events. Without a layer that correlates both, critical signals are missed.This is precisely where the ROC delivers its core value. By maintaining a unified data lake fed by both NOC and SOC telemetry and applying continuous AI-driven analysis, the ROC provides the cross-domain intelligence that allows teams to collaborate effectively and resolve complex, multi-dimensional incidents faster and more accurately than any siloed approach could achieve.
Building Your Operations Centre Strategy
Not every organisation needs to build all three centres simultaneously. The right approach depends on the organisation’s size, industry, regulatory environment, and operational maturity.For most enterprises, the NOC is the foundational layer. It provides the core operational capability upon which SOC and ROC functions can be built. The SOC is typically the second priority, driven by the increasing prevalence and sophistication of cyber threats and the regulatory requirements that mandate security monitoring capabilities.The ROC is the convergence layer that realises the full potential of the NOC and SOC. Organisations that have invested in both infrastructure and security operations — and are experiencing the friction, blind spots, and response delays that come from siloed data — are the natural candidates for ROC adoption. For organisations where technology risk spans both domains simultaneously, the ROC becomes an operational necessity rather than an optional enhancement.
→ Request an operational maturity assessmentCommon Anti-Patterns in Operations Centre Design
As enterprises build and evolve their operations centres, several anti-patterns frequently emerge that undermine effectiveness. Recognising and avoiding these patterns is as important as understanding the ideal structure.The first anti-pattern is treating operations centres as cost centres rather than value centres. When ROC, NOC, and SOC functions are viewed purely through a cost lens, organisations chronically underinvest in tooling, talent, and training. The result is operations teams that are perpetually reactive, understaffed, and unable to deliver the proactive, strategic value that mature operations centres provide.The second anti-pattern is building isolated NOC and SOC functions with no shared data or convergence layer. When the NOC and SOC operate with completely separate tooling, separate incident management processes, and no mechanism to correlate their data, cross-domain incidents become organisational nightmares. This is the problem the ROC is specifically designed to solve. Teams spend more time coordinating across silos than resolving the actual issue. Information is lost in translation. Accountability becomes unclear.The third anti-pattern is attempting to combine all three functions into a single, undifferentiated operations team. While convergence through the ROC is essential, each centre requires specialised skills, tooling, and operational focus. Blending them into a single undifferentiated team typically results in security being deprioritised during high-volume infrastructure incidents, AI-driven correlation being de-prioritised in favour of manual firefighting, and operators being expected to maintain expertise across too many domains without the structural support to do so effectively.
The Future: Converged Operations with Specialised Functions
The most effective model emerging among leading enterprises is one built around the ROC as the convergence engine: a unified operational data platform, continuously fed by the NOC and SOC, with AI driving correlation, insight, and resolution across domains.In this model, the NOC retains its domain specialisation in infrastructure availability and performance. The SOC retains its domain specialisation in threat detection and response. But the ROC ensures that no incident falls through the cracks between them and that when complex, multi-domain incidents occur, the organisation has both the data and the AI-driven intelligence to respond decisively.This is not a future state. Enterprises that have adopted this model are already seeing measurable improvements in MTTD, MTTR, and operational resilience. The question is not whether to build toward converged operations, but how quickly the organisation can close the gap between its current siloed model and this integrated ideal.